In the landscape of modern project management, uncertainty is the only certainty. For leaders who prioritize stability and predictability, risk can feel like a constant threat to success. However, risk is not merely a negative force to be eliminated; it is an inherent component of any endeavor that involves change. Understanding the mechanics of risk allows risk-averse leaders to navigate uncertainty with precision rather than fear.
This guide provides a deep dive into the components of risk management. It moves beyond surface-level definitions to explore the structural elements that define how projects handle uncertainty. Whether you are managing a software rollout, a construction initiative, or a strategic shift, the principles outlined here remain constant. We will examine identification, analysis, response, and monitoring through a lens that respects the need for stability while acknowledging the necessity of forward motion.
Defining Risk Tolerance and Appetite 🎯
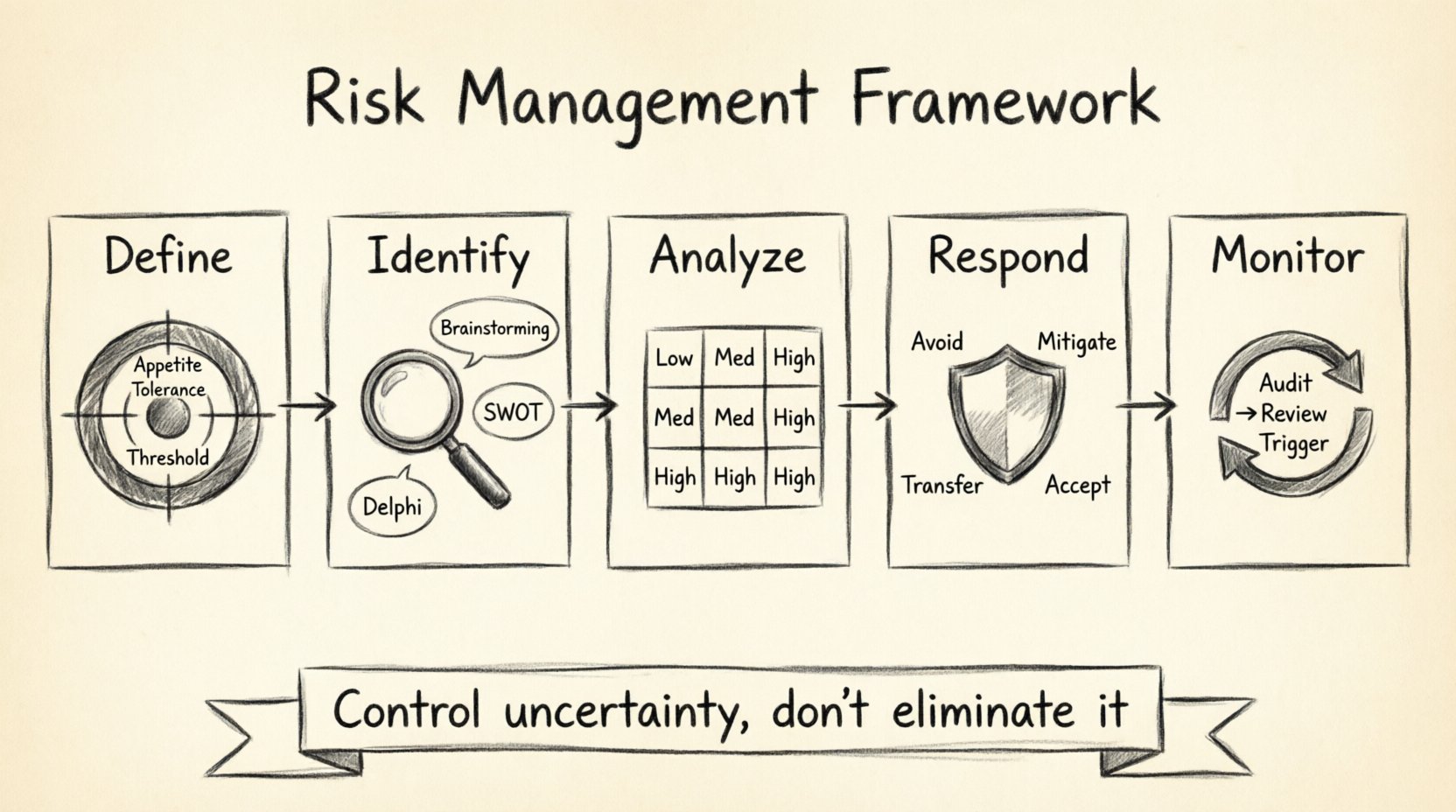
Before implementing any controls, a leader must understand their own position regarding uncertainty. Risk tolerance and risk appetite are distinct concepts that often get conflated. Grasping this distinction is the first step toward a mature risk framework.
- Risk Appetite: This refers to the amount and type of risk that an organization or leader is willing to pursue or retain. It is a strategic choice. For example, a startup might have a high appetite for financial risk to achieve rapid market penetration, whereas a healthcare provider might have a low appetite due to regulatory constraints.
- Risk Tolerance: This defines the specific degree of variability in objectives that a leader is willing to accept. It is often quantifiable. If a project budget has a 5% variance tolerance, that is a hard limit.
- Risk Threshold: A specific point at which a risk is considered unacceptable. Crossing this threshold triggers mandatory action.
For risk-averse leaders, these definitions serve as guardrails. They prevent the paralysis of indecision by setting clear boundaries. When you know your threshold, you do not need to analyze every minor fluctuation. You focus your energy where it matters most.
Consider the following breakdown of how these concepts interact with project phases:
- Initiation: Define the appetite based on organizational goals.
- Planning: Set thresholds for budget, schedule, and scope.
- Execution: Monitor against these thresholds continuously.
- Closing: Review actual variances against the initial appetite to refine future estimates.
By establishing these parameters early, you create a baseline against which all future risks can be measured. This reduces emotional decision-making during crises.
The Identification Phase: Seeing Around Corners 🔍
Identification is the foundation of risk management. If a risk is not identified, it cannot be managed. For leaders who prefer predictability, the unknown is the primary source of anxiety. Therefore, the identification process must be systematic, thorough, and repeatable.
Techniques for Comprehensive Identification
There is no single method that captures all risks. A robust approach combines several techniques to ensure coverage across different dimensions of the project.
- Brainstorming Sessions: Gather the team to list potential risks. Encourage diverse perspectives. Sometimes the person furthest from the core task sees the biggest threat.
- SWOT Analysis: Review Strengths, Weaknesses, Opportunities, and Threats. This helps contextualize internal weaknesses against external threats.
- Delphi Technique: Use anonymous expert surveys to reach a consensus on risks without groupthink influencing the results.
- Root Cause Analysis: Look at past issues in similar projects. What went wrong last time? It is likely to go wrong again.
- Assumption Analysis: Challenge every assumption made in the project plan. If an assumption proves false, what is the impact?
When identifying risks, categorize them to make the list manageable. Common categories include:
- Technical risks (feasibility, technology maturity)
- Management risks (resource availability, planning accuracy)
- External risks (regulatory changes, market shifts)
- Organizational risks (budget cuts, priority changes)
Document every identified risk in a central location. This document, often called a Risk Register, becomes the living record of the project’s uncertainty. It ensures that no risk is lost in conversation or email chains.
Analysis: Probability and Impact ⚖️
Once risks are identified, they must be analyzed. Not all risks require the same level of attention. A minor delay in a non-critical path activity differs vastly from a potential supplier bankruptcy. Analysis allows you to prioritize your efforts.
Qualitative Analysis
Qualitative analysis is the most common method for initial screening. It relies on subjective judgment to estimate the likelihood and impact of each risk.
- Probability: How likely is the risk to occur? (Low, Medium, High)
- Impact: What is the consequence if it occurs? (Negligible, Moderate, Severe)
Combining these two factors creates a risk score. This score helps determine which risks need immediate attention. For risk-averse leaders, this scoring system provides a logical justification for resource allocation. It removes the guesswork from prioritization.
Quantitative Analysis
For high-stakes risks, qualitative measures may not be sufficient. Quantitative analysis uses numerical data to estimate the potential effect of risks on project objectives. This often involves:
- Monte Carlo Simulations: Running thousands of simulations to predict the probability of completing the project within a specific budget or timeline.
- Decision Tree Analysis: Using a diagram to evaluate different courses of action and their potential outcomes based on probability and cost.
- Expected Monetary Value (EMV): Calculating the average outcome when the future includes scenarios that may or may not happen.
While quantitative analysis requires more data and time, it offers a higher degree of confidence. It allows leaders to state, “There is a 90% chance we will finish within budget,” rather than relying on intuition.
Response Strategies: From Avoidance to Acceptance 🛡️
Once risks are prioritized, the next step is deciding how to handle them. There are four primary strategies for addressing threats. Each strategy carries different implications for resources and timeline.
The table below outlines the core strategies and their typical applications.
| Strategy | Definition | When to Use |
|---|---|---|
| Avoid | Eliminate the threat entirely. | When the risk is too severe and cannot be tolerated. |
| Mitigate | Reduce the probability or impact. | When the risk is significant but cannot be fully avoided. |
| Transfer | Shift the risk to a third party. | When specialized expertise is needed or cost of ownership is too high. |
| Accept | Acknowledge the risk and prepare a contingency. | When the cost of action outweighs the potential loss. |
Deep Dive into Mitigation
Mitigation is the most active strategy. It involves taking steps to reduce the likelihood of the risk or lessen its impact. Examples include:
- Conducting additional testing to reduce technical failure probability.
- Adding buffers to the schedule to account for potential delays.
- Implementing stricter quality control processes.
- Training team members to reduce human error.
For risk-averse leaders, mitigation offers the best balance. It acknowledges the risk exists but actively works to shrink its footprint. It is not about eliminating uncertainty, but shrinking its size to a manageable level.
Understanding Contingency Plans
Acceptance does not mean ignoring the risk. It means having a plan ready if the risk materializes. This is known as a contingency plan. It is distinct from a workaround, which is a reactive measure taken after the event. A contingency plan is proactive.
- Contingency Reserve: A specific allocation of budget or time set aside for known risks.
- Management Reserve: A buffer for unknown risks that may arise during the project.
Defining when to trigger these reserves is crucial. Leaders must establish clear triggers. For example, “If the supplier misses the delivery date by 5 days, we activate the backup vendor contingency.” This prevents delay in decision-making during a crisis.
Continuous Monitoring and Control 🔄
Risk management is not a one-time activity. It is a continuous process that runs from the start of the project to its end. The project environment changes, and so do the risks. New risks emerge while others may fade away.
Risk Audits
Regular audits ensure that the risk management plan is working as intended. An audit asks questions like:
- Are the identified risks still relevant?
- Are the response strategies effective?
- Is the risk register up to date?
- Are stakeholders aware of the current risk status?
These audits provide an opportunity to correct course. If a mitigation strategy is not reducing the risk as expected, a new approach must be devised.
Risk Reviews
Unlike audits, which are often formal, risk reviews are integrated into regular project meetings. They keep risk top-of-mind for the team. During these reviews:
- Check the status of high-priority risks.
- Identify new risks that have appeared since the last meeting.
- Update probability and impact assessments based on new information.
- Verify that contingency reserves are being used correctly.
Consistency is key. If risk is only discussed at major milestones, the project becomes reactive. By discussing it weekly or bi-weekly, the team maintains a state of readiness.
Tracking Triggers
Every risk response strategy should have a trigger. A trigger is a warning sign that indicates a risk is about to occur or has occurred. Monitoring these triggers allows the team to act before the risk causes damage.
Examples of triggers include:
- A specific date approaching without a milestone completion.
- A cost variance exceeding a certain percentage.
- A key team member resigning.
- Changes in regulatory compliance requirements.
By tracking these indicators, leaders can transition from reacting to events to anticipating them.
Building a Resilient Risk Culture 🤝
Even the best tools and processes fail if the culture does not support them. In many organizations, risk is associated with failure. This mindset discourages team members from reporting potential issues. For risk-averse leaders, this is a critical challenge to address.
Psychological Safety
Team members must feel safe reporting risks without fear of retribution. If a team member hides a problem because they fear being blamed, the project is at greater risk. Leaders must foster an environment where transparency is rewarded.
- Encourage Open Communication: Make it clear that reporting a risk is a positive action, not a negative one.
- Focus on the Problem, Not the Person: When a risk materializes, focus on fixing the issue rather than assigning blame.
- Lead by Example: Admit your own uncertainties. If the leader hides their doubts, the team will follow suit.
Stakeholder Engagement
Risk management extends beyond the project team. Stakeholders often hold the key to risk mitigation. They may provide resources, approve changes, or offer guidance. Keeping them informed is essential.
- Regular Reporting: Provide clear, concise updates on risk status.
- Transparency: Do not hide negative risks. Stakeholders prefer to know early so they can prepare.
- Expectation Management: Ensure stakeholders understand the trade-offs between risk, cost, and time.
When stakeholders are engaged, they become partners in risk management. They understand that uncertainty is part of the process and support the necessary buffers and contingencies.
Common Pitfalls to Avoid ⚠️
Even experienced leaders make mistakes in risk management. Recognizing these pitfalls helps you steer clear of them.
- Risk Bias: Focusing only on negative risks. Opportunities are also risks. A positive risk might mean finishing early or under budget.
- Analysis Paralysis: Spending too much time analyzing risks and not enough time executing the project. Balance is required.
- Static Registers: Treating the Risk Register as a document to be created once. It must be dynamic and updated regularly.
- Ignoring Low Probability Risks: Sometimes low probability risks have catastrophic impact. Do not dismiss them solely based on likelihood.
- Lack of Ownership: Every risk must have an owner. If no one is responsible, no one will manage it.
Final Thoughts on Managing Uncertainty 🚀
Managing risk is not about creating a perfect plan that never changes. It is about building a system that can adapt when things do not go according to plan. For risk-averse leaders, the goal is not to eliminate risk, but to control it.
By understanding tolerance, identifying threats systematically, analyzing impact, and implementing robust response strategies, you create a stable foundation for your projects. This stability does not come from avoiding uncertainty, but from having the tools to handle it.
The components outlined here provide a framework for consistency. When you apply these principles, you reduce the anxiety associated with the unknown. You allow your team to focus on execution, knowing that the risks are being monitored and managed. This is the essence of modern project management: navigating the future with confidence and clarity.
Remember that every project is unique. Adapt these components to fit your specific context. The principles remain, but the application may vary. Stay vigilant, stay informed, and keep the lines of communication open. This approach will serve you well in any endeavor.