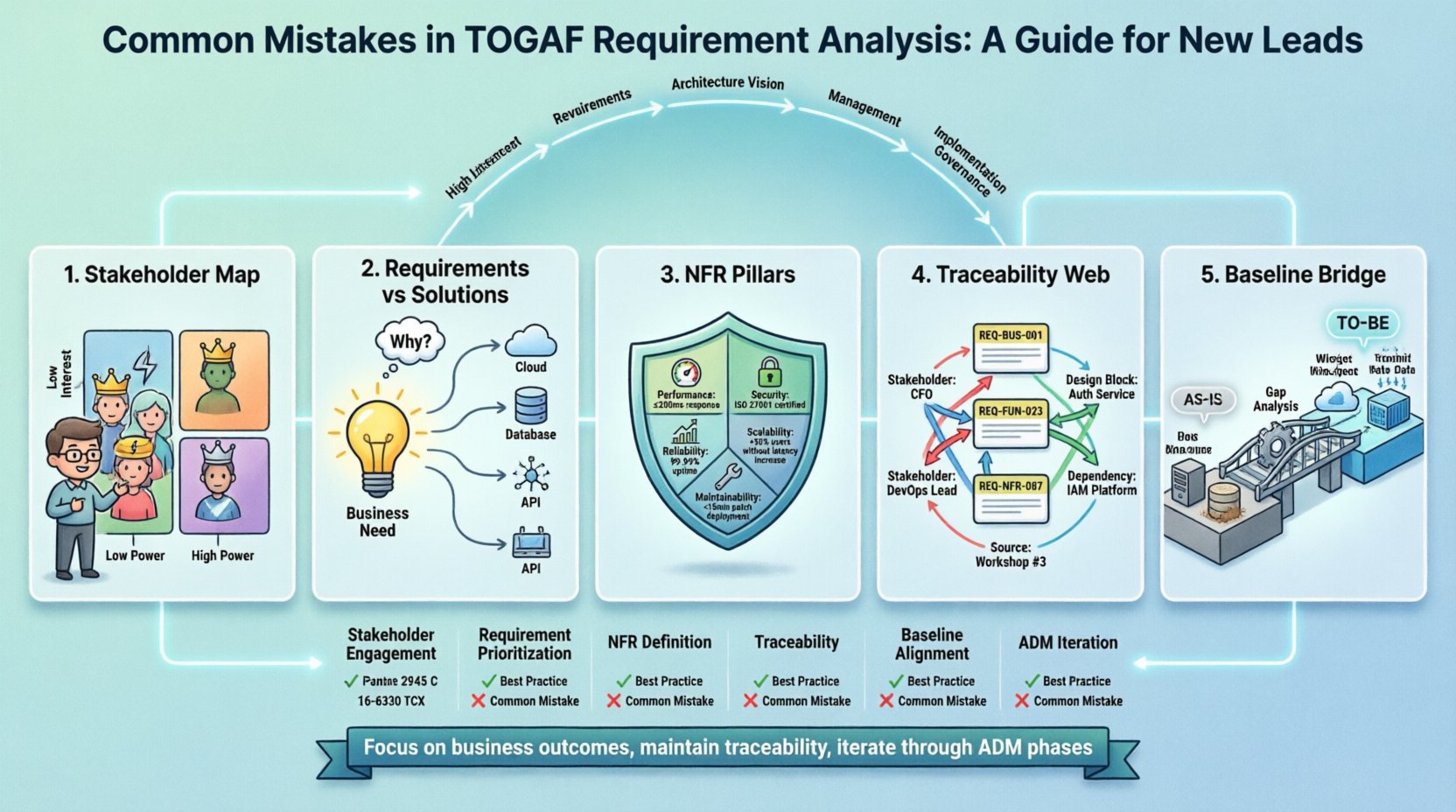
Entering the role of an enterprise architecture lead requires a shift in mindset from tactical execution to strategic oversight. Within the TOGAF framework, the architecture development method (ADM) provides a structured approach, yet the phase of requirement analysis often becomes a stumbling block for those new to the discipline. Requirement analysis is not merely about gathering a list of needs; it is about establishing a clear, traceable link between business goals and technical capabilities. When this link is weak, the entire architecture initiative risks divergence from organizational value.
This guide addresses the frequent errors encountered during TOGAF requirement analysis. By understanding these pitfalls, new leads can navigate the complexity of the ADM cycle with greater precision. The focus here is on practical application, stakeholder engagement, and the structural integrity of the architecture repository.
🔍 The Foundation of Requirement Analysis in TOGAF
Requirement analysis within TOGAF spans several phases, most notably Phase A (Architecture Vision), Phase B (Business Architecture), Phase C (Information Systems Architectures), and Phase D (Technology Architecture). Each phase introduces specific types of requirements that must be captured, validated, and maintained.
Effective analysis relies on three core pillars:
- Business Requirements: High-level goals and constraints defined by the organization’s strategy.
- Stakeholder Concerns: Specific interests held by individuals or groups influencing the architecture.
- Non-Functional Requirements: Quality attributes such as performance, security, and reliability.
Failure to distinguish between these categories often leads to scope creep and architectural drift. New leads must ensure that the requirement repository is populated correctly before moving to the design phases.
❌ Mistake 1: Ignoring Stakeholder Context and Power Dynamics
One of the most frequent errors involves treating all stakeholders as equals in the requirements gathering process. In reality, influence and interest vary significantly across an organization. A lead might spend hours interviewing a mid-level manager while a critical decision-maker remains silent.
The Impact
When key stakeholders are not identified early, their concerns are often overlooked until late in the project. This results in rework, as the architecture must be adjusted to accommodate requirements that were previously unspoken. Furthermore, it can lead to a lack of sponsorship for the architecture initiative, causing resources to be withdrawn.
Remediation Strategy
To avoid this, construct a comprehensive stakeholder map at the beginning of the Architecture Vision phase. This map should categorize stakeholders based on their power and interest.
- High Power, High Interest: Engage closely and manage expectations rigorously.
- High Power, Low Interest: Keep satisfied by providing high-level updates.
- Low Power, High Interest: Keep informed to prevent misinformation.
- Low Power, Low Interest: Monitor with minimal effort.
Do not assume that the title of a role indicates their influence. In some organizations, a technical lead may have more sway over implementation than a nominal department head. Interviews must be structured to uncover these hidden dynamics.
❌ Mistake 2: Confusing Requirements with Solutions
New leads often fall into the trap of documenting solutions as requirements. For example, a stakeholder might say, “We need a new database system.” If the architect records this as a requirement, the analysis becomes biased toward that specific technology before the actual need is understood.
The Impact
This premature commitment limits the solution space. The architecture may lock in a technology that is no longer viable, or one that does not meet the underlying business need. It also creates technical debt, as the architecture is forced to support a specific tool rather than a functional capability.
Remediation Strategy
Apply the “Why” technique. Whenever a solution is proposed, ask why that solution is necessary.
- Stakeholder: “We need a cloud storage solution.”
- Architect: “What business capability is this supporting?”
- Stakeholder: “We need to share large files securely with partners.”
- Architect: “So the requirement is secure file transfer, not specifically cloud storage.”
Document the underlying capability (secure file transfer) rather than the proposed tool. This allows for flexibility in selecting the best technology during the later phases of the ADM cycle.
❌ Mistake 3: Neglecting Non-Functional Requirements (NFRs)
Functional requirements describe what the system does. Non-functional requirements describe how the system performs. New leads often prioritize the “what” and ignore the “how,” assuming that performance and security will be handled by the implementation team.
The Impact
Architectures built without defined NFRs often fail under load or become vulnerable to security breaches. Compliance requirements, such as data residency or audit trails, are also NFRs. Missing these in the analysis phase means the architecture cannot be approved by legal or compliance boards later.
Remediation Strategy
Establish a standard set of NFR categories that must be addressed for every architecture project. Common categories include:
- Performance: Response times, throughput, and latency.
- Security: Authentication, authorization, and encryption standards.
- Reliability: Availability targets and disaster recovery capabilities.
- Scalability: The ability to handle growth in data or users.
- Maintainability: Ease of updates and patching.
These should be quantified where possible. Instead of “fast performance,” specify “95% of transactions must complete within 200 milliseconds.” Quantification removes ambiguity and allows for objective testing later.
❌ Mistake 4: Poor Traceability Between Requirements
Traceability refers to the ability to link a requirement back to its source and forward to the design elements that satisfy it. Without this, it is impossible to know if a specific design decision actually addresses a business need.
The Impact
When traceability is lost, the architecture becomes a black box. Auditors cannot verify compliance. Change managers cannot assess the impact of a modification because they do not know which requirements are affected. This leads to “shadow architecture,” where undocumented workarounds proliferate.
Remediation Strategy
Implement a Requirement Repository. This is a structured database or document management system where every requirement is assigned a unique identifier (e.g., REQ-BUS-001).
For each requirement, maintain the following links:
- Source: Which stakeholder or business goal initiated this?
- Dependency: Which other requirements must be met first?
- Satisfaction: Which architecture building block or design element satisfies this?
- Status: Is the requirement accepted, rejected, or deferred?
Review this repository regularly during the ADM cycle. If a requirement is not linked to a design element, it should be flagged as unsatisfied. If a design element is not linked to a requirement, it is a candidate for removal to reduce complexity.
❌ Mistake 5: Skipping the Baseline Analysis
The baseline represents the current state of the organization’s architecture. Many leads rush to define the target state without fully documenting the existing capabilities, gaps, and technical debt.
The Impact
Without a baseline, it is impossible to measure progress. Migration strategies become guesswork. You may inadvertently design a target state that relies on capabilities that no longer exist or are being decommissioned. This leads to a failed migration plan.
Remediation Strategy
Conduct a thorough inventory of the current environment. This does not require a full audit of every server, but it does require a high-level view of:
- Applications: What systems are currently in use?
- Infrastructure: What hardware or cloud resources support them?
- Processes: How is work actually done today?
- Data: Where does critical information reside?
Document the known limitations and pain points. These become the drivers for the new architecture. If a current system is slow, the new architecture must explicitly address the performance bottleneck. If a process is manual, the new architecture should aim to automate it.
📊 Comparison of Common Errors vs. Best Practices
To visualize the differences between ineffective analysis and robust architecture planning, consider the following comparison table.
| Area | Common Mistake | Best Practice |
|---|---|---|
| Stakeholders | Interviewing everyone equally | Mapping power and interest; engaging key decision-makers first |
| Requirements | Recording proposed solutions | Recording underlying business needs and capabilities |
| Quality Attributes | Ignoring performance and security | Defining quantifiable non-functional requirements early |
| Traceability | Unlinked requirements and designs | Using a repository with unique IDs and bidirectional links |
| Current State | Rushing to the target state | Documenting the baseline to identify gaps and migration paths |
| Documentation | Using informal notes | Maintaining a formal architecture repository |
🔗 Integrating Analysis into the ADM Cycle
Requirement analysis is not a one-time event. It is an iterative process that spans the ADM cycle. As the architecture evolves, new requirements may emerge, and old ones may become obsolete.
Phase A: Architecture Vision
Here, the primary focus is on high-level business requirements and stakeholder concerns. The goal is to define the scope of the project and the principles that will guide the architecture.
Phase B & C: Business and Information Systems
Detailed business requirements are gathered here. Functional requirements for data and applications are defined. This is where the distinction between business capability and IT capability becomes critical.
Phase D: Technology Architecture
Technical requirements are refined. NFRs are specified in detail. The baseline technology stack is analyzed to determine what can be reused.
Phases E through H: Implementation and Governance
Requirements are validated against the implemented solution. Gaps are identified, and change requests are managed. The requirement repository is updated to reflect the as-built state.
🛠️ Communication Protocols for New Leads
Technical accuracy is only half the battle. Communication ensures that the analysis is understood and accepted across the organization.
- Use Visual Models: Diagrams are often more effective than text. Use process flows or capability maps to illustrate requirements.
- Define Terminology: Ensure all stakeholders agree on the meaning of key terms. “Availability” means different things to IT and Operations.
- Regular Reviews: Schedule periodic requirement review meetings. Do not wait until the end of the project to validate the list.
- Feedback Loops: Create a mechanism for stakeholders to request changes to requirements without disrupting the entire process.
🚦 Moving Forward with Confidence
The path to effective architecture is paved with clear requirements. By avoiding the common traps of solution bias, poor stakeholder mapping, and neglected traceability, new leads can build architectures that are resilient and aligned with business strategy. The TOGAF framework provides the structure, but the discipline of the analyst provides the value.
Focus on the business outcomes rather than the technology. Ensure every requirement has a purpose and a link to a design element. Maintain the repository with rigor. These practices will establish a foundation of trust between the architecture team and the rest of the organization.
Remember that architecture is a journey, not a destination. The requirement analysis phase sets the direction. If the direction is clear, the journey will be smoother. If the direction is ambiguous, the team will wander. Invest the time to get it right from the start.

