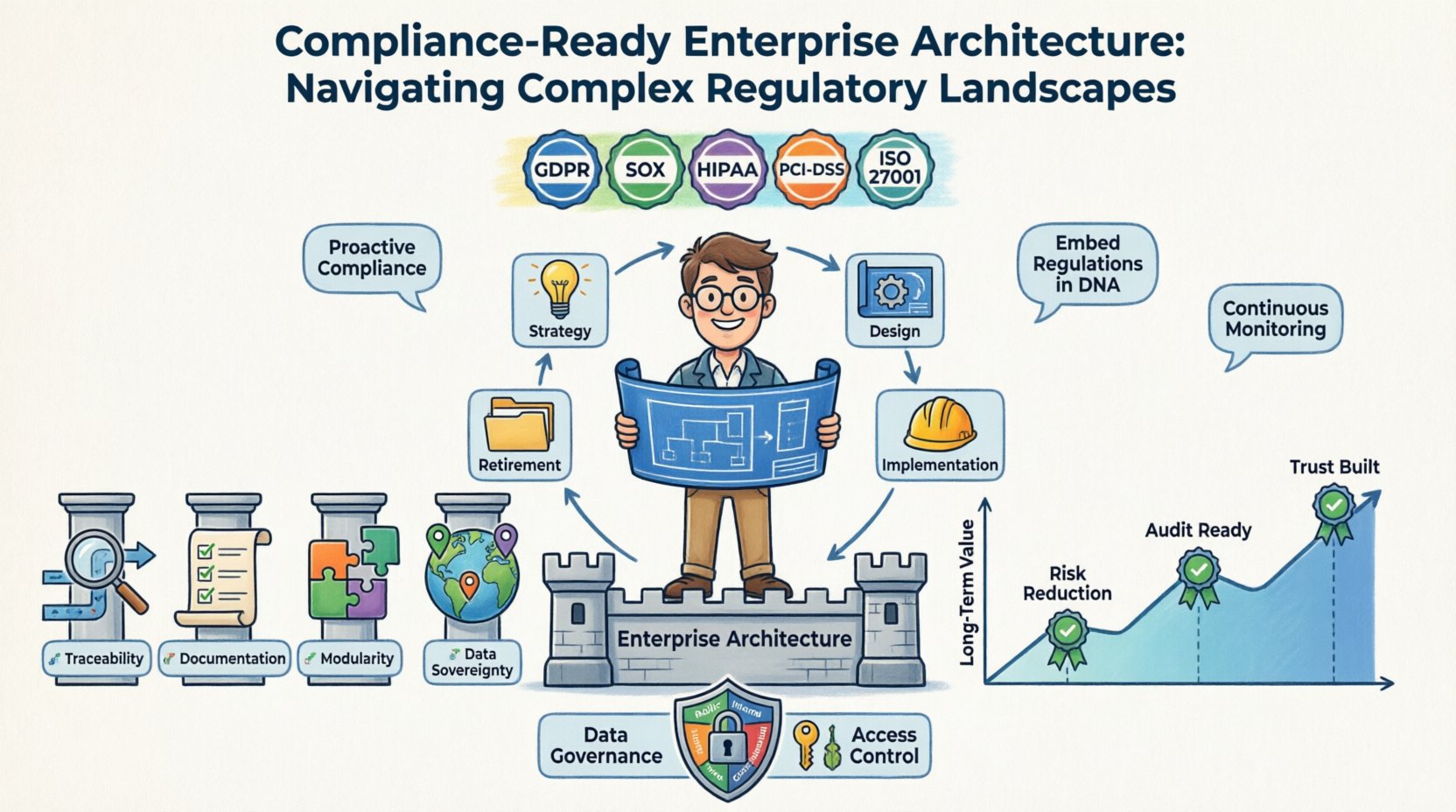
In the modern digital economy, the intersection of technology and regulation has become increasingly intricate. Organizations are no longer just building systems to support business functions; they are constructing digital environments that must withstand rigorous scrutiny from global regulatory bodies. Enterprise Architecture (EA) serves as the backbone for this endeavor, providing the necessary structure to integrate compliance requirements directly into the design and operation of IT systems. A compliance-ready enterprise architecture ensures that legal obligations are not treated as afterthoughts but are embedded into the core DNA of the organization’s technology stack.
This guide explores the methodologies required to build an architecture that is resilient to regulatory shifts. It addresses the challenges of data privacy, financial reporting, and sector-specific mandates. By adopting a proactive stance, enterprises can mitigate risk, reduce audit friction, and maintain operational continuity amidst a volatile regulatory environment.
🌐 The Regulatory Maze: Understanding the Challenge
The landscape of regulatory compliance is fragmented and dynamic. What constitutes adherence today may be insufficient tomorrow. Enterprises operate across multiple jurisdictions, each with its own set of laws governing data, finance, security, and privacy. Ignoring these nuances can lead to severe penalties, reputational damage, and operational halts.
Key regulatory drivers include:
- General Data Protection Regulation (GDPR): Governs how personal data of EU citizens is handled, emphasizing consent, right to erasure, and data portability.
- Sarbanes-Oxley Act (SOX): Mandates strict financial reporting standards and internal controls for public companies in the United States.
- Health Insurance Portability and Accountability Act (HIPAA): Protects sensitive patient health information in the healthcare sector.
- Payment Card Industry Data Security Standard (PCI-DSS): Ensures secure handling of credit card information.
- California Consumer Privacy Act (CCPA): Extends data privacy rights to California residents, similar to GDPR but with specific state-level nuances.
Each of these frameworks imposes unique technical requirements. For instance, GDPR requires data minimization, while SOX demands immutable audit trails. Enterprise Architecture must reconcile these often conflicting demands without fragmenting the technology landscape.
🧱 Pillars of a Compliant Architecture
To achieve compliance readiness, the architecture must rest on specific foundational pillars. These principles guide the design decisions, ensuring that every component contributes to the overall compliance posture.
1. End-to-End Traceability 🔗
Every data element and business process must be traceable. If a regulatory body asks where specific customer data originated or how a financial transaction was processed, the architecture must provide the answer instantly. This requires maintaining clear lineage maps that connect data sources to consumption points.
2. Documentation and Standardization 📝
Compliance is often about evidence. Architects must ensure that design decisions, security controls, and data flows are documented rigorously. Standardized patterns reduce ambiguity and make it easier to demonstrate adherence during audits.
3. Modularity and Abstraction 🧩
Regulations change frequently. An architecture built on rigid, monolithic structures is difficult to adapt. Modularity allows teams to swap out components that do not meet new standards without rebuilding the entire system. Abstraction layers hide complex compliance logic from the business logic, making updates less invasive.
4. Data Sovereignty and Localization 🌍
Many regulations dictate where data can physically reside. The architecture must support geo-replication and data residency controls to ensure information stays within approved borders. This often requires a distributed design that respects jurisdictional boundaries.
⚙️ Integrating Compliance into the EA Lifecycle
Compliance cannot be bolted onto a finished system. It must be woven into the entire Enterprise Architecture lifecycle. This ensures that governance is proactive rather than reactive.
- Strategy and Planning: Regulatory requirements are identified early. Compliance goals are set alongside business objectives. This phase involves mapping laws to business capabilities.
- Architecture Design: Controls are designed into the solution. Security patterns, encryption standards, and access controls are selected based on the regulatory context. Architecture Decision Records (ADRs) document why specific compliance choices were made.
- Implementation: Development teams follow the architectural blueprints. Automated testing ensures that code adheres to security and privacy standards before deployment.
- Operations and Monitoring: Continuous monitoring detects deviations from the compliance baseline. Alerts trigger when data flows breach boundaries or access patterns become suspicious.
- Retirement: When systems are decommissioned, data must be disposed of securely in accordance with retention policies. The architecture ensures data is wiped or archived correctly.
📋 Key Frameworks and Standards Comparison
Understanding the nuances of different frameworks helps architects select the right controls. The table below outlines the primary focus areas for major standards.
| Framework | Primary Focus | Key Architectural Requirement | Typical Industry |
|---|---|---|---|
| GDPR | Personal Data Privacy | Consent management, Data Erasure mechanisms | All (EU operations) |
| SOX | Financial Reporting | Immutable Audit Logs, Access Controls | Public Companies |
| HIPAA | Health Information | Encryption at Rest/Transit, Role-Based Access | Healthcare |
| PCI-DSS | Payment Security | Network Segmentation, Tokenization | Retail / Finance |
| ISO 27001 | Information Security | Security Management System, Risk Assessment | All |
Architects must cross-reference these requirements to find overlaps. For example, an organization handling both financial data and health information must satisfy both SOX and HIPAA, which share common needs for access control and logging.
🔒 Data Governance and Privacy Engineering
Data is the central asset in most regulatory frameworks. Governance is the policy layer, while privacy engineering is the technical implementation. Together, they form the shield around sensitive information.
Classification and Tagging
Not all data carries the same risk. An architecture should automatically classify data based on sensitivity. Personally Identifiable Information (PII) requires stricter handling than public marketing data. Automated tagging ensures that downstream systems treat this data appropriately.
Encryption and Tokenization
Encryption renders data unreadable to unauthorized users. It is essential for data both in transit and at rest. Tokenization replaces sensitive data with non-sensitive equivalents, reducing the scope of compliance audits. If a tokenized database is compromised, the actual data remains safe.
Access Control Models
Zero Trust principles apply heavily here. Access should be granted on a need-to-know basis. Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) help enforce these policies programmatically. Regular reviews of user permissions prevent privilege creep.
Data Retention Policies
Regulations often dictate how long data must be kept and when it must be destroyed. The architecture must enforce automated retention schedules. This prevents the accumulation of data that poses unnecessary risk or liability.
🛡️ Auditability and Risk Management
Compliance is often verified through audits. The architecture must facilitate this process by making evidence collection seamless. Manual evidence gathering is prone to error and delays.
- Centralized Logging: All critical actions should generate logs. These logs must be centralized to prevent tampering. They should capture who did what, when, and from where.
- Immutable Storage: Log storage should be write-once-read-many (WORM). This ensures that historical records cannot be altered to hide non-compliance.
- Real-Time Monitoring: Automated tools should scan for anomalies. Unusual access patterns or data exfiltration attempts should trigger immediate alerts.
- Risk Assessment Integration: Architecture decisions should be linked to risk registers. High-risk components require more rigorous testing and oversight.
By embedding these capabilities, the organization shifts from a reactive audit stance to a continuous compliance model. This reduces the stress and cost associated with periodic external reviews.
🔮 Adapting to Future Regulations
The regulatory environment is not static. New technologies bring new risks. Artificial Intelligence, cloud computing, and the Internet of Things (IoT) introduce novel compliance challenges.
AI and Algorithmic Accountability
Emerging regulations regarding AI focus on bias, transparency, and explainability. Architecture must support model governance. This includes versioning of algorithms, tracking training data sources, and ensuring decisions can be explained to auditors.
Cloud and Third-Party Risk
As organizations move to the cloud, they inherit the responsibilities of their providers. However, compliance remains the customer’s responsibility. Architectures must clearly define the shared responsibility model. Contracts and technical controls must align with the chosen cloud environment.
Global Data Flows
Data localization laws are becoming more common. Cross-border data transfers require specific legal mechanisms and technical safeguards. Architectures must support data residency controls that prevent unauthorized movement across borders.
🤝 Building a Compliance Culture within Architecture Teams
Technology alone cannot solve compliance issues. The people designing and building the systems must understand the regulatory context. Training and collaboration are essential.
- Regular Training: Architects and developers need ongoing education on new laws. Compliance officers should be part of the design review process.
- Shared Responsibility: Compliance is not just a legal team function. It is a shared burden across IT, operations, and business units.
- Feedback Loops: Audits should result in architectural improvements. Lessons learned from past findings must be incorporated into future designs.
Fostering a culture where compliance is seen as a quality attribute rather than a constraint leads to better outcomes. When teams understand the “why” behind the rules, they build better systems.
📈 Sustaining Long-Term Value
Building a compliance-ready enterprise architecture is an investment in stability. It reduces the risk of fines and legal action. It builds trust with customers and partners. It streamlines the path to new markets by pre-empting regulatory hurdles.
Organizations that prioritize this approach gain a competitive advantage. They can scale faster because they are not constantly retrofitting systems to meet new laws. The architecture evolves with the business, ensuring that growth does not come at the cost of security or legality.
Ultimately, the goal is resilience. A resilient architecture withstands regulatory storms. It allows the organization to focus on innovation while the underlying structure ensures adherence to the law. By following these principles, enterprises can navigate the complex regulatory landscape with confidence and clarity.