The digital landscape is evolving at an unprecedented pace, and with it, the threat surface expands daily. For Chief Information Officers (CIOs), the challenge is no longer just about maintaining uptime or optimizing performance. It is about ensuring the resilience of the entire enterprise ecosystem against sophisticated adversaries. Security-first architecture represents a fundamental shift from reactive patching to proactive design. This approach embeds security controls directly into the foundational layers of enterprise architecture, ensuring that risk management is not an afterthought but a core tenet of business strategy.
Implementing this model requires a deep understanding of modern threats, a commitment to strategic alignment, and a willingness to restructure traditional workflows. The following guide details the essential components of building a robust security posture that protects assets while enabling innovation.
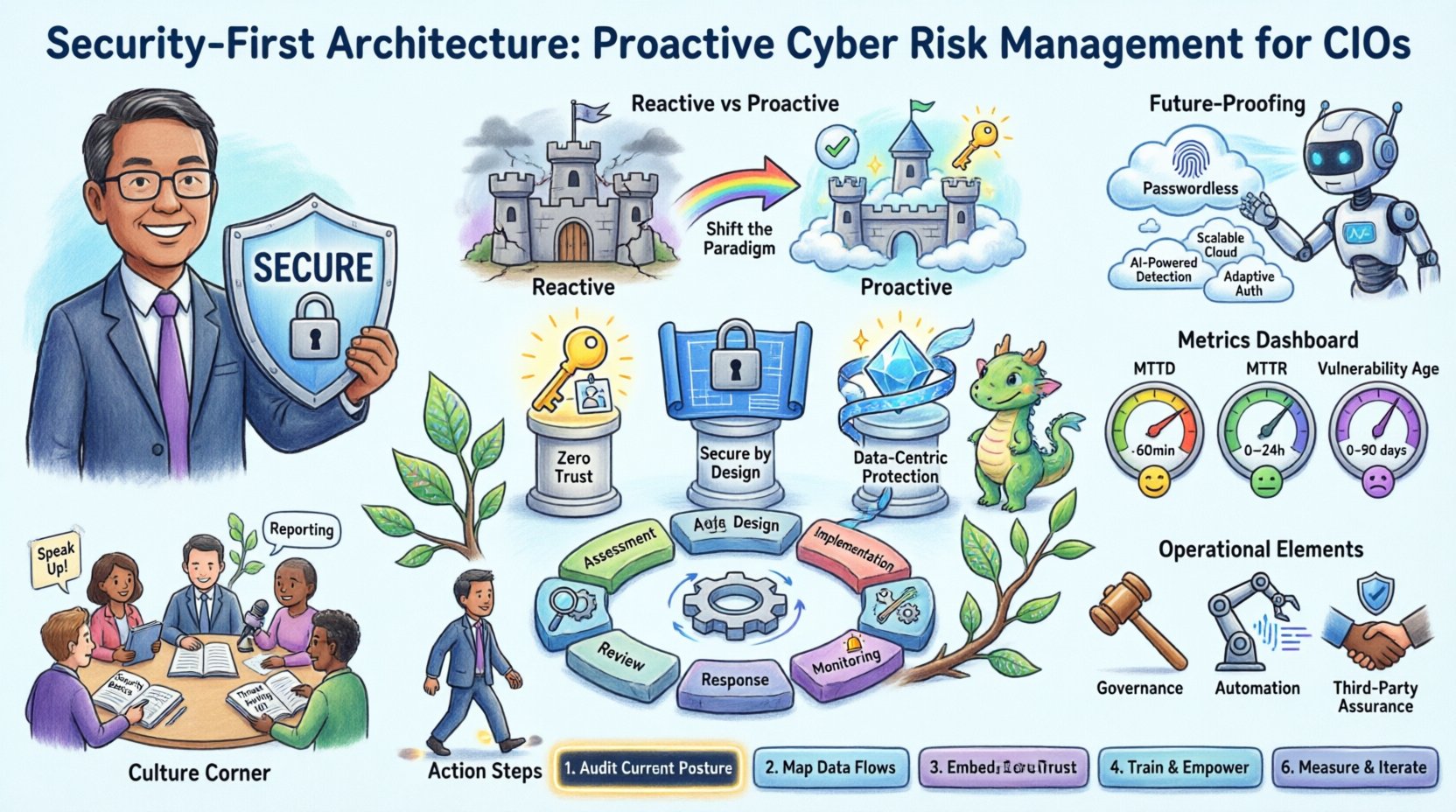
🔄 The Paradigm Shift: Reactive vs. Proactive
Traditional IT strategies often treated security as a perimeter defense. Firewalls and access controls were placed at the edge, with the assumption that everything inside was trusted. This model has collapsed under the weight of cloud adoption, remote work, and complex supply chains. Attackers no longer need to breach the perimeter; they only need one compromised endpoint to gain lateral movement.
Proactive cyber risk management addresses this by assuming breach is inevitable. The focus shifts to detection, containment, and rapid recovery. This requires a mindset change across the organization, moving security from a gatekeeping function to an enabling one.
Key Differences in Approach
Legacy Model: Defend the perimeter, trust internal traffic, patch after vulnerability disclosure.
Security-First Model: Verify every transaction, assume internal threats, patch before vulnerability disclosure.
Legacy Model: Security is a cost center and compliance burden.
Security-First Model: Security is a competitive advantage and business enabler.
Legacy Model: Siloed teams with distinct responsibilities.
Security-First Model: Cross-functional collaboration between architects, developers, and operations.
🏗️ Foundational Pillars of Security-First Architecture
Building a resilient architecture requires adherence to specific principles. These principles guide decision-making at every stage of the enterprise lifecycle, from initial design to decommissioning.
1. Zero Trust Network Access
The Zero Trust model operates on the premise of “never trust, always verify.” Identity and device health become the new perimeter. Every access request, regardless of origin, must be authenticated, authorized, and encrypted.
Least Privilege: Users and systems receive only the access necessary to perform their tasks.
Micro-segmentation: Network traffic is restricted to specific zones, limiting lateral movement.
Continuous Validation: Trust is not granted once; it is re-evaluated continuously based on behavior.
2. Secure by Design
Security requirements must be integrated into the design phase of every project. Waiting until the deployment phase to add security controls often leads to technical debt and compromised functionality.
Threat Modeling: Identify potential attack vectors during the planning stage.
Secure Coding Standards: Enforce guidelines that prevent common vulnerabilities like injection flaws.
Supply Chain Verification: Validate third-party components before integration.
3. Data-Centric Protection
Data is the crown jewel of any enterprise. Protecting data regardless of where it resides or how it moves is critical.
Classification: Tag data based on sensitivity and regulatory requirements.
Encryption: Encrypt data at rest and in transit.
DLP: Implement controls to prevent unauthorized exfiltration.
📊 Strategic Framework for Risk Management
CIOs must translate technical principles into a strategic framework. This framework aligns security investments with business objectives. The table below outlines the core phases of this framework and their corresponding actions.
Phase | Objective | Key Activities | Stakeholders |
|---|---|---|---|
Assessment | Identify Assets & Threats | Asset inventory, vulnerability scanning, risk mapping | Architects, Security Analysts |
Design | Embed Controls | Threat modeling, architecture review, policy definition | Enterprise Architects, DevOps |
Implementation | Deploy Safely | Configuration management, automated testing, access provisioning | IT Operations, Developers |
Monitoring | Detect Anomalies | Log aggregation, SIEM analysis, behavioral analytics | SOC Team, CISO |
Response | Contain & Recover | Incident playbooks, backup restoration, forensics | Incident Response, Legal |
Review | Improve & Adapt | Post-incident analysis, policy updates, training | Management, HR, Security |
🔍 Operationalizing the Security Strategy
Strategy without execution is merely a statement. CIOs must establish operational processes that ensure security principles are applied consistently.
1. Governance and Policy
Clear governance structures define who is responsible for what. Policies must be actionable and not just theoretical documents. They should cover data handling, access management, and incident response.
Roles and Responsibilities: Define specific duties for data owners, custodians, and processors.
Compliance Alignment: Ensure policies meet regulatory standards such as GDPR, HIPAA, or SOC 2.
Audit Trails: Maintain logs of policy enforcement and exceptions.
2. Automation and Orchestration
Manual security processes are slow and prone to error. Automation allows for rapid response to threats and consistent enforcement of policies.
Infrastructure as Code (IaC): Define infrastructure using code to ensure security configurations are replicated automatically.
Continuous Integration/Continuous Deployment (CI/CD): Integrate security scans into the build pipeline to catch issues early.
SOAR: Use Security Orchestration, Automation, and Response platforms to streamline incident handling.
3. Third-Party Risk Management
Modern enterprises rely heavily on vendors and partners. A breach in the supply chain can compromise the entire organization.
Vetting: Assess vendor security posture before onboarding.
Contractual Obligations: Include security clauses in service level agreements.
Monitoring: Continuously monitor vendor access and activity.
👥 Leadership and Culture
Technology alone cannot secure an enterprise. The human element is often the weakest link. CIOs must foster a culture where security is everyone’s responsibility.
1. Security Awareness Training
Regular training keeps employees informed about current threats. Training should be engaging and relevant to specific roles.
Phishing Simulations: Test employee vigilance against social engineering.
Role-Based Training: Provide specific guidance for developers, HR, and finance teams.
Reporting Mechanisms: Create easy channels for reporting suspicious activity.
2. Incentives and Accountability
Security should be a shared goal. Incorporate security metrics into performance reviews to encourage accountability.
KPIs: Track metrics like patch latency, incident response time, and training completion.
Recognition: Acknowledge teams that demonstrate strong security practices.
Blame-Free Reporting: Encourage reporting of mistakes to facilitate learning rather than punishment.
📈 Measuring Success
To manage risk effectively, you must measure it. Key Performance Indicators (KPIs) provide visibility into the health of the security posture.
Essential Metrics
Mean Time to Detect (MTTD): How long it takes to identify a threat.
Mean Time to Respond (MTTR): How long it takes to mitigate a threat.
Vulnerability Age: The average time a vulnerability remains unpatched.
Compliance Status: Percentage of systems meeting security standards.
Incident Cost: Financial impact of security events.
🔮 Future-Proofing the Architecture
The threat landscape is dynamic. New technologies like quantum computing and AI introduce both new capabilities and new risks. A security-first architecture must be adaptable.
Emerging Considerations
AI Security: Protect models from poisoning and ensure they do not leak sensitive data.
Cloud Evolution: Adapt to serverless and multi-cloud environments.
Identity Evolution: Move towards passwordless authentication and biometric verification.
Privacy Engineering: Build privacy features into systems by default.
🚀 Moving Forward: Actionable Steps for CIOs
Implementing this architecture is a journey, not a destination. CIOs can take the following steps to begin the transition immediately.
Conduct a Gap Analysis: Compare current architecture against security-first principles.
Establish a Center of Excellence: Create a dedicated team to drive security strategy.
Invest in Talent: Hire and train staff in modern security practices.
Prioritize Debt Reduction: Allocate resources to fix critical legacy vulnerabilities.
Engage the Board: Ensure executive leadership understands and supports the risk strategy.
The path to a secure enterprise requires discipline, investment, and continuous attention. By embedding security into the DNA of the organization, CIOs can protect their assets while driving innovation. The goal is not just to prevent breaches, but to build systems that remain functional and trustworthy even when under attack.
Proactive cyber risk management is the only viable strategy for modern enterprises. It transforms security from a cost into a strategic asset, ensuring long-term viability in an increasingly hostile digital environment.