Enterprise IT landscapes are evolving rapidly. Organizations are moving beyond single-cloud or on-premises silos to embrace hybrid cloud architectures. This approach combines private infrastructure with public cloud services, offering flexibility and resilience. However, simply connecting environments is not enough. Effective hybrid cloud architecture strategy requires deliberate planning for workload placement and management.
This guide explores the critical components of building a robust hybrid environment. We focus on technical decisions, governance models, and operational practices that drive efficiency. Our goal is to provide a clear path for architects and engineering leaders.
Understanding the Hybrid Cloud Landscape 🌐
A hybrid cloud environment connects on-premises data centers with one or more public cloud platforms. This connectivity allows data and applications to be shared between them. The primary benefit is the ability to maintain control over sensitive data while leveraging the scalability of public resources.
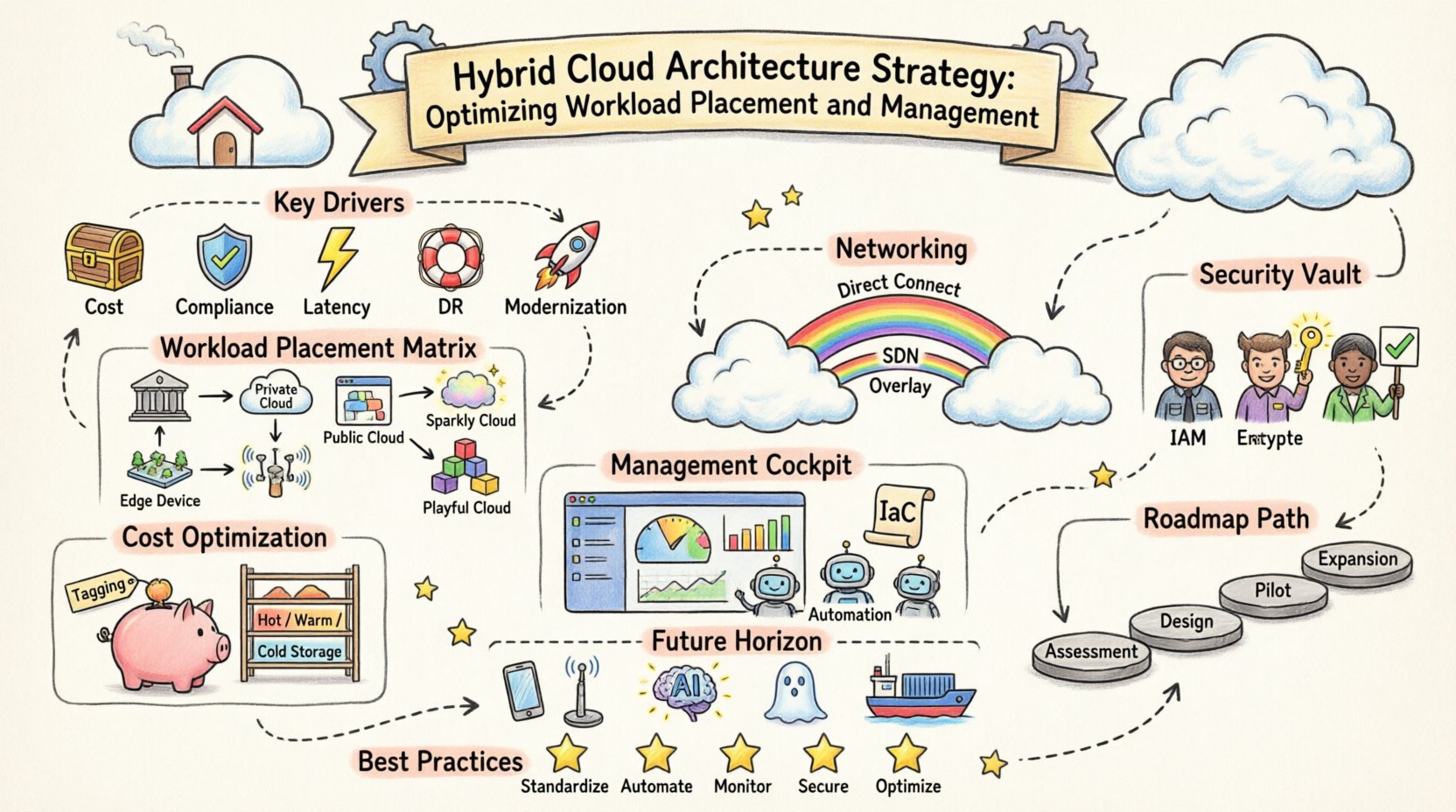
Key Drivers for Adoption
- Cost Optimization: Balance fixed infrastructure costs with variable cloud spending.
- Compliance and Data Sovereignty: Keep regulated data on-premises while processing elsewhere.
- Latency Requirements: Process data closer to the source when low latency is critical.
- Disaster Recovery: Utilize cloud regions for backup and failover capabilities.
- Legacy Modernization: Gradually migrate workloads without a “big bang” approach.
Workload Classification and Placement 📊
Not every application fits every environment. A strategic approach involves classifying workloads based on specific technical and business requirements. This classification informs where resources should reside.
Placement Criteria
When deciding where to host a workload, evaluate the following factors:
- Latency Sensitivity: Applications requiring real-time response often stay on-premises or at the edge.
- Compliance Needs: Data subject to strict regulations may require physical control.
- Cost Structure: Steady-state workloads often benefit from reserved capacity on-premises.
- Scalability Demand: Bursty workloads are ideal for public cloud elasticity.
- Data Gravity: Moving large datasets over the network is expensive; process near the data.
- Dependency Management: Consider how tightly coupled services are to underlying hardware.
Workload Placement Matrix
| Workload Type | Primary Location | Key Reason |
|---|---|---|
| Core Banking Systems | Private Cloud / On-Premises | Strict Compliance & Data Control |
| Customer Facing Web Apps | Public Cloud | Scalability & Global Reach |
| Big Data Analytics | Public Cloud (Cloud-Native) | Compute Power & Storage Elasticity |
| IoT Data Processing | Edge / On-Premises | Low Latency & Bandwidth Savings |
| Development Environments | Public Cloud | Rapid Provisioning & Cost Efficiency |
Networking and Connectivity 🌉
Connectivity is the backbone of hybrid architecture. If the network is slow or unstable, the architecture fails. Establishing reliable links between private and public environments is paramount.
Connection Models
- Direct Connect: Dedicated physical links offer higher throughput and lower latency than public internet paths.
- Software-Defined Networking (SDN): Enables dynamic routing and policy enforcement across boundaries.
- Overlay Networks: Virtual networks that abstract underlying physical infrastructure for easier management.
- Multi-Cloud Routing: Intelligent traffic steering to avoid bottlenecks and optimize costs.
Bandwidth Management
Network capacity planning must account for data synchronization and failover scenarios. Over-provisioning ensures stability during peak loads. Compression and deduplication techniques can reduce the volume of data transferred, lowering costs.
Security and Governance 🔒
Security in a hybrid environment is more complex than in a single-cloud setup. The perimeter has expanded, requiring a zero-trust approach.
Identity and Access Management (IAM)
- Unified Identity: Use a single source of truth for user credentials across all environments.
- Role-Based Access Control (RBAC): Define permissions based on job function, not just environment.
- Multi-Factor Authentication (MFA): Enforce MFA for all administrative access points.
- Privileged Access Management: Monitor and record sessions for high-privilege accounts.
Data Protection
Data encryption must be consistent whether at rest or in transit. Key management systems should be centralized to avoid key silos. Regular audits ensure that security policies are applied uniformly across on-premises and cloud segments.
Compliance Automation
Automated compliance checks reduce the risk of human error. Continuous monitoring tools should alert teams when configurations drift from policy standards.
Management and Orchestration ⚙️
Managing disparate environments requires a unified control plane. Without orchestration, operations become fragmented and error-prone.
Unified Monitoring
- Centralized Logging: Aggregate logs from all sources into a single repository for analysis.
- Performance Metrics: Track latency, throughput, and resource utilization across boundaries.
- Alerting: Configure notifications based on thresholds that apply to the entire system.
Automation and Infrastructure as Code
Manual configuration leads to drift and inconsistencies. Infrastructure as Code (IaC) allows teams to define resources in text files. This approach ensures repeatability and version control.
- Provisioning: Automate the creation of servers, storage, and networks.
- Configuration Management: Ensure software states match desired definitions.
- Pipeline Integration: Embed deployment logic into CI/CD workflows.
Cost Optimization 💰
Hybrid cloud can save money, but it can also introduce complexity costs. Financial operations (FinOps) practices help align spending with value.
Cost Allocation
- Tagging Strategies: Tag resources to track spending by department, project, or application.
- Chargeback Models: Implement internal billing to make teams accountable for their usage.
- Resource Rightsizing: Regularly review instance sizes to match actual demand.
Storage Tiering
Not all data needs high-speed access. Move cold data to cheaper storage tiers. Archive old logs or backups to long-term storage solutions to reduce active storage costs.
Operational Challenges and Mitigation 🛠️
Implementing this strategy introduces specific challenges. Understanding these risks allows for better preparation.
Skills Gap
- Teams often specialize in either on-premises or cloud technologies.
- Cross-training is essential for staff to manage the hybrid boundary.
- Consider hiring specialists in cloud networking and security.
Complexity
- More components mean more potential points of failure.
- Standardization reduces complexity. Avoid custom integrations where possible.
- Document architecture decisions clearly for future reference.
Vendor Lock-in
- Proprietary services can make migration difficult.
- Prefer open standards and containerized workloads for portability.
- Design for multi-cloud compatibility from the start.
Implementation Roadmap 🗺️
A phased approach reduces risk. Start small and expand as capabilities mature.
Phase 1: Assessment
- Inventory existing applications and infrastructure.
- Identify dependencies and data flows.
- Define business requirements and constraints.
Phase 2: Design
- Architect the connectivity model.
- Select the management platform.
- Define security policies and governance rules.
Phase 3: Pilot
- Migrate a non-critical workload.
- Test monitoring and backup procedures.
- Gather feedback and adjust the design.
Phase 4: Expansion
- Scale the architecture to more workloads.
- Implement full automation pipelines.
- Optimize costs based on usage data.
Future Considerations 🔮
The hybrid landscape continues to evolve. Staying informed helps maintain a competitive edge.
- Edge Computing: Processing moves closer to devices, requiring new hybrid models.
- AI Integration: Machine learning workloads often require specialized hardware availability.
- Serverless Adoption: Event-driven architectures simplify management but require new networking strategies.
- Containerization: Standardizing on container formats improves portability across environments.
Summary of Best Practices ✅
- Standardize: Use consistent tools and protocols across all environments.
- Automate: Reduce manual intervention to minimize errors and speed up deployment.
- Monitor: Gain visibility into performance and security across the entire stack.
- Secure: Apply zero-trust principles to every connection and transaction.
- Optimize: Regularly review costs and performance to ensure alignment with business goals.
Building a successful hybrid cloud architecture is a journey, not a destination. It requires continuous adjustment based on business needs and technological advances. By following these strategic guidelines, organizations can build resilient, efficient, and secure environments.

