In the modern digital landscape, the ability to connect disparate systems quickly and reliably is no longer a technical luxury; it is a fundamental business requirement. Organizations today operate within complex ecosystems where data flows between legacy mainframes, cloud-native microservices, third-party SaaS applications, and internal databases. The architecture that manages these connections determines whether an enterprise moves with the speed of the market or struggles under the weight of its own complexity. 📉
Building a robust Enterprise API Strategy is the process of defining how these connections are created, governed, and maintained. It goes beyond simple connectivity. It involves establishing patterns, security protocols, and lifecycle management practices that ensure integration layers support business agility rather than hinder it. This guide explores the critical components of designing effective integration architectures.
🎯 Defining the Core Strategy
An API strategy is not merely a technical specification; it is a business enabler. It dictates how information is exposed and consumed across the organization. Without a clear strategy, integration efforts often devolve into point-to-point connections that create a “spaghetti architecture.” This state makes maintenance difficult, security auditing complex, and scalability nearly impossible.
Effective strategy development requires alignment between IT leadership and business stakeholders. The goal is to treat APIs as products. This means considering the developer experience, the stability of the interface, and the value the API delivers to consumers, whether they are internal teams or external partners.
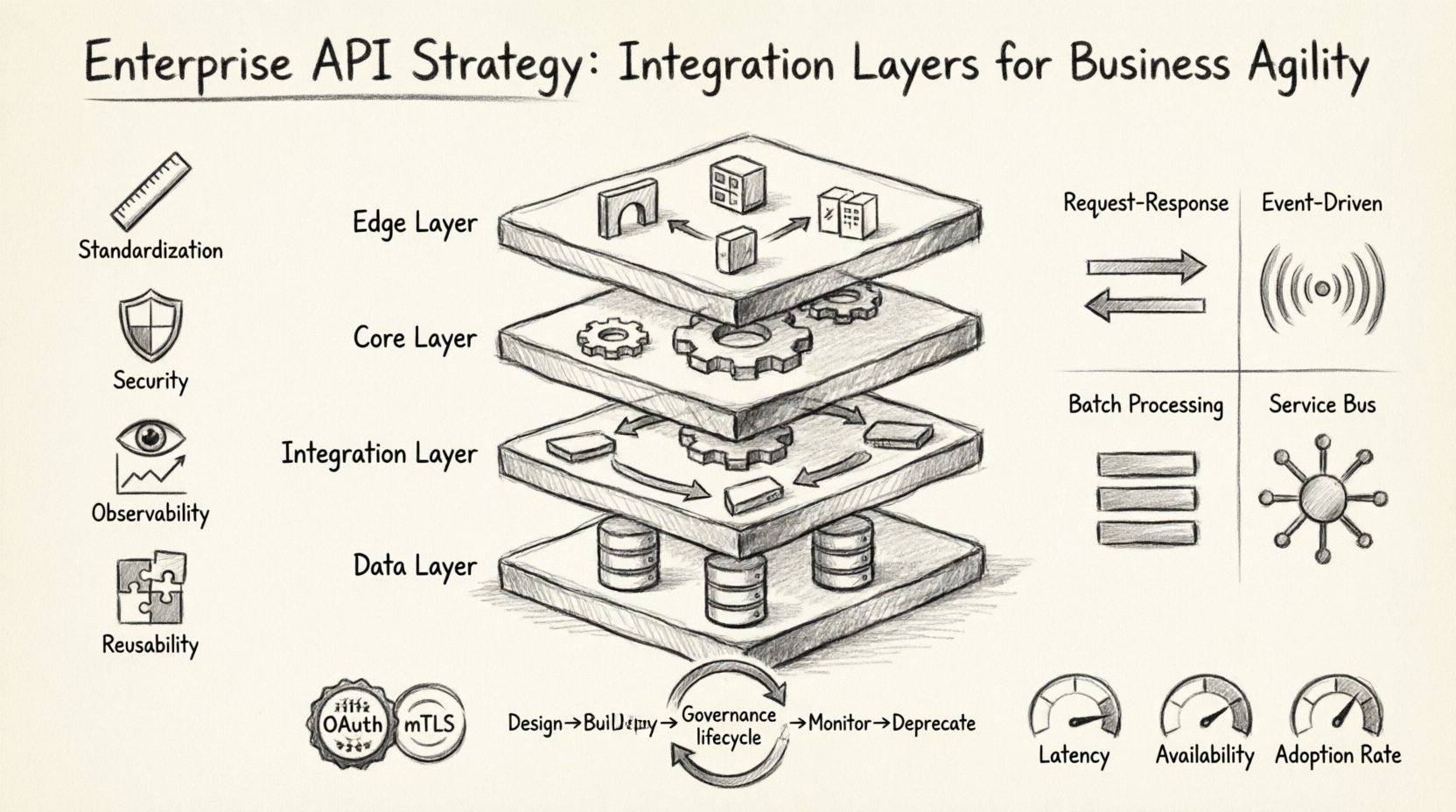
Key Pillars of API Strategy
- Standardization: Establishing consistent naming conventions, versioning schemes, and error handling across all services.
- Security: Implementing uniform authentication and authorization protocols that do not compromise performance.
- Observability: Ensuring every API call is logged, monitored, and analyzed to detect issues early.
- Reusability: Designing services that can be composed to form new capabilities without rebuilding from scratch.
🧱 Designing the Integration Layers
To achieve scalability and resilience, integration should not be a flat plane. Instead, it requires a layered approach. This structure isolates concerns, allowing changes in one layer to occur without destabilizing the entire system. A well-designed architecture typically consists of four distinct layers: the Edge, the Core, the Integration, and the Data Layer.
1. The Edge Layer (Entry Point)
This is the first point of contact for external traffic. It acts as the gatekeeper. Its primary responsibilities include routing, rate limiting, and initial security validation. By handling these tasks here, the internal systems remain protected from overload and malicious traffic.
- Function: Load balancing, SSL termination, and API Gateway management.
- Benefit: Insulates backend services from direct internet exposure.
2. The Core Layer (Business Logic)
Once traffic passes the edge, it reaches the core. This layer houses the actual business logic and domain-specific services. It should be designed to be stateless where possible to facilitate horizontal scaling. The core layer communicates with the integration layer but does not handle low-level transport concerns.
- Function: Executing specific business rules and transaction processing.
- Benefit: Decouples business logic from infrastructure concerns.
3. The Integration Layer (Orchestration)
This is the glue that holds the architecture together. It handles data transformation, protocol translation, and workflow orchestration. When a request comes in, it might need to traverse multiple systems to fulfill a single user action. The integration layer manages this choreography.
- Function: Message transformation, protocol bridging, and workflow management.
- Benefit: Allows heterogeneous systems to communicate seamlessly.
4. The Data Layer (Persistence)
The foundation of the architecture. This layer manages how data is stored, retrieved, and managed. In a modern strategy, this layer supports both traditional relational databases and newer data stores optimized for specific workloads like caching or analytics.
- Function: Data persistence, caching, and retrieval.
- Benefit: Ensures data integrity and availability.
📊 Comparison of Integration Patterns
Selecting the right integration pattern is crucial for performance and maintainability. Different scenarios require different approaches. The table below outlines common patterns and their ideal use cases.
| Pattern | Description | Best Use Case |
|---|---|---|
| Request-Response | Client sends a request and waits for an immediate response. | Synchronous operations, user-facing dashboards. |
| Event-Driven | Services emit events that other services consume asynchronously. | High-volume data processing, real-time updates. |
| Batch Processing | Data is collected and processed in large groups at scheduled intervals. | End-of-day reporting, data synchronization. |
| Service Bus | A central communication backbone for routing messages between services. | Complex enterprise ecosystems with many moving parts. |
🛡️ Security and Compliance
Security cannot be an afterthought in an API strategy. Every exposed endpoint is a potential entry point for attackers. A comprehensive security model must address authentication, authorization, data protection, and compliance requirements.
Authentication and Authorization
Implementing robust identity management is non-negotiable. The industry standard for this is OAuth 2.0 and OpenID Connect. These protocols allow for secure delegation of access without sharing credentials. Organizations should adopt the principle of least privilege, ensuring that API consumers only have access to the specific data and actions required for their function.
- API Keys: Simple but less secure; best for internal or trusted services.
- OAuth Tokens: Industry standard for third-party access and user delegation.
- mTLS: Mutual TLS authentication for high-security internal service-to-service communication.
Data Protection
Encryption must be applied both in transit and at rest. TLS 1.3 is the current standard for securing data in transit. For data at rest, encryption keys must be managed securely, often using a centralized key management service. Additionally, data masking should be applied in logs and non-production environments to prevent accidental exposure of sensitive information.
Compliance Considerations
Depending on the industry, regulations such as GDPR, HIPAA, or PCI-DSS may apply. An API strategy must include mechanisms to support data subject requests, such as the right to be forgotten. Audit trails are essential to demonstrate compliance during regulatory reviews. Every access event must be logged with sufficient context to trace who accessed what data and when.
⚙️ Governance and Lifecycle Management
Without governance, an API strategy becomes chaotic. Governance ensures that APIs adhere to standards, remain secure, and provide value over time. It involves managing the lifecycle of an API from conception to retirement.
The API Lifecycle
- Design: Defining the contract before code is written. Using tools like OpenAPI specifications ensures clarity between consumers and producers.
- Build: Developing the service according to the design. Automated testing ensures quality gates are met.
- Deploy: Releasing the API to the target environment. Blue-green deployments can minimize downtime during updates.
- Monitor: Tracking performance, errors, and usage patterns continuously.
- Deprecate: Planning the retirement of old versions to encourage migration to newer, more efficient implementations.
Versioning Strategies
Breaking changes are inevitable. How an organization handles versioning dictates how easily consumers can update their integrations. Common strategies include:
- URI Versioning: Including the version number in the URL path (e.g.,
/v1/resource). - Header Versioning: Specifying the version in the request headers.
- Content Negotiation: Using the
Acceptheader to define the media type version.
Each strategy has trade-offs. URI versioning is explicit and easy to debug, while header versioning keeps URLs clean but requires careful client configuration.
📈 Measuring Success and Agility
To validate the effectiveness of the integration strategy, organizations must define clear Key Performance Indicators (KPIs). These metrics provide visibility into the health and value of the API ecosystem.
Technical Metrics
- Latency: The time taken for a request to complete. High latency indicates bottlenecks.
- Availability: The percentage of time the API is operational. Aim for 99.9% or higher for critical services.
- Error Rate: The frequency of 4xx and 5xx responses. Sudden spikes indicate deployment issues or attacks.
Business Metrics
- Adoption Rate: How many developers or partners are using the API.
- Time-to-Market: How quickly new features can be integrated into the system.
- Cost Efficiency: The reduction in maintenance costs due to reuse and standardization.
🚀 Future-Proofing the Architecture
The technology landscape evolves rapidly. An architecture designed today must remain viable in five or ten years. This requires a focus on abstraction and flexibility. Avoid tight coupling between components. Ensure that the underlying technology stack can be swapped without requiring a complete rewrite of the business logic.
Embracing cloud-native principles, such as containerization and orchestration, allows for greater elasticity. However, the fundamental principles of good API design remain constant. Clear contracts, robust error handling, and comprehensive documentation are timeless assets. By prioritizing these fundamentals, organizations build a foundation that can adapt to new technologies as they emerge.
🔄 Moving Forward
Implementing an Enterprise API Strategy is a journey, not a destination. It requires continuous refinement as the business grows and technology advances. The goal is to create an environment where innovation can flourish without being stifled by technical debt.
By adhering to structured design patterns, enforcing rigorous security standards, and maintaining clear governance, enterprises can achieve the agility they need to compete in a digital-first world. The integration layer becomes a strategic asset, enabling rapid deployment of new capabilities and seamless data flow across the entire organization. This approach transforms integration from a cost center into a driver of value.