The transition from traditional on-premises infrastructure to cloud-native environments represents a fundamental shift in how organizations operate. It is not merely a technology migration; it is a strategic evolution. Enterprise Architecture (EA) serves as the blueprint for this transformation, ensuring that every investment aligns with long-term business goals while maintaining the agility required to compete in a digital economy.
Adopting a cloud-first mindset requires a delicate balance. On one side lies the demand for rapid innovation and scalability. On the other stands the necessity for rigorous control, security, and cost management. This guide explores the structural and operational components necessary to build a robust cloud-first enterprise architecture.
Defining Cloud-First Enterprise Architecture 🧭
Cloud-first enterprise architecture refers to a strategic approach where cloud-based solutions are the default choice for all new digital initiatives. It does not imply that every workload must move to the public cloud immediately, but rather that the cloud is the primary environment considered during the design phase.
Key characteristics include:
- Resilience by Design: Systems are built to tolerate failures without human intervention.
- Decoupled Services: Applications are modular, allowing independent scaling and updates.
- Automation: Infrastructure and processes are managed through code to reduce manual error.
- Data-Centricity: Data is treated as a core asset, accessible across boundaries securely.
Unlike legacy architectures that often rely on monolithic structures, cloud-first designs prioritize microservices and API-driven interactions. This shift enables teams to deploy changes faster while isolating risks to specific components rather than the entire system.
Core Architectural Principles 🛠️
To maintain flexibility without sacrificing stability, architects must adhere to a set of foundational principles. These principles guide decision-making when selecting technologies and designing workflows.
1. Scalability and Elasticity
Infrastructure must scale dynamically to match demand. This involves both vertical scaling (increasing capacity of a single node) and horizontal scaling (adding more nodes). Cloud-native systems utilize auto-scaling groups to handle traffic spikes automatically, ensuring performance remains consistent during peak usage.
2. Interoperability and Portability
Reliance on a single vendor creates risk. A strategic architecture avoids proprietary lock-in by using open standards and containerization. This ensures that workloads can be moved between different cloud environments or back to on-premises systems if business requirements change.
3. Security as a Foundation
Security is not an add-on layer but an integral part of the architecture. Identity and Access Management (IAM) must be centralized, and data encryption should be applied at rest and in transit. Zero Trust principles ensure that no user or system is trusted by default, even if they are inside the network perimeter.
4. Observability
Traditional monitoring is often insufficient for complex cloud environments. Observability provides deep insights into system behavior through logs, metrics, and traces. It allows teams to understand not just that a failure occurred, but why it happened and how to prevent it.
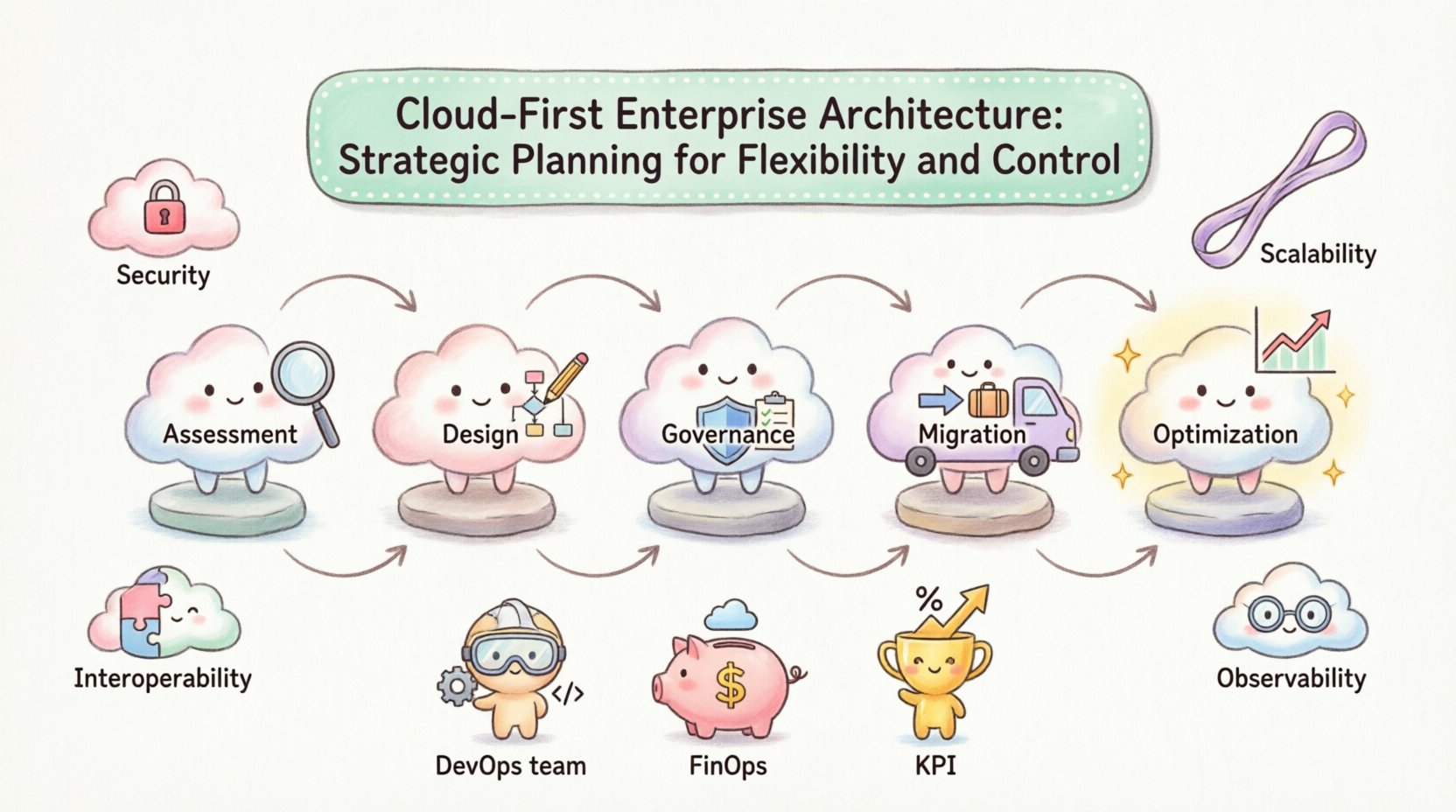
Strategic Planning Framework 📋
Successful implementation requires a phased approach. Rushing into the cloud without a roadmap often leads to technical debt and budget overruns. The following framework outlines the critical stages of planning.
Phase 1: Assessment and Discovery
Before moving workloads, organizations must understand their current state. This involves inventorying existing applications, data flows, and dependencies.
- Application Portfolio Analysis: Categorize applications based on their suitability for cloud migration (e.g., rehost, refactor, replace).
- Dependency Mapping: Identify how applications interact with each other to avoid breaking critical links during migration.
- Compliance Review: Determine regulatory requirements regarding data residency and privacy.
Phase 2: Target Architecture Design
Once the current state is understood, the future state is defined. This involves selecting the appropriate cloud models (public, private, or hybrid) and designing the network topology.
- Network Segmentation: Design Virtual Private Clouds (VPCs) to isolate workloads by function or sensitivity.
- Identity Federation: Establish a single sign-on mechanism that integrates with existing directory services.
- Data Strategy: Define where data resides, how it is backed up, and the recovery objectives.
Phase 3: Governance and Policy Definition
Control mechanisms must be established before deployment begins. Policies define what is allowed and what is prohibited within the environment.
- Resource Tagging Standards: Enforce consistent naming and tagging for cost allocation and management.
- Change Management: Define approval workflows for infrastructure changes.
- Guardrails: Implement automated checks that prevent the creation of non-compliant resources.
Phase 4: Implementation and Migration
This phase involves the actual movement of workloads. It should follow an iterative approach, starting with low-risk applications to validate the processes.
- Pilot Migration: Move a non-critical workload to test the pipeline.
- Hybrid Connectivity: Establish secure connections (such as dedicated links) between on-premises data centers and cloud environments.
- Data Synchronization: Ensure data consistency during the transition period.
Phase 5: Optimization and Operations
Post-migration, the focus shifts to ongoing management and optimization. This includes monitoring performance, managing costs, and refining the architecture based on usage patterns.
| Planning Stage | Key Objective | Primary Deliverable |
|---|---|---|
| Assessment | Understand current capabilities | Inventory Report & Risk Analysis |
| Design | Define target state | Architecture Diagram & Standards |
| Migration | Execute transfer | Migrated Workloads & Validation Logs |
| Optimization | Improve efficiency | Cost Reports & Performance Metrics |
Governance and Control Mechanisms ⚖️
Flexibility can lead to chaos if left unchecked. Effective governance ensures that the cloud environment remains secure, compliant, and cost-effective. This requires a shift from manual oversight to automated enforcement.
Policy as Code
Traditional policies stored in documents are often ignored or misunderstood. Policy as Code translates rules into executable scripts that run continuously. If a developer attempts to create a storage volume that is unencrypted, the system blocks the action automatically.
- Automated Compliance Checks: Scan environments regularly for deviations from security baselines.
- Drift Detection: Identify when live infrastructure differs from the defined configuration.
- Enforcement Modes: Choose between blocking (prevention) or auditing (logging) based on the criticality of the resource.
Identity and Access Management (IAM)
Access control is the first line of defense. The principle of least privilege ensures that users and services have only the permissions necessary to perform their tasks.
- Role-Based Access Control (RBAC): Assign permissions based on job functions rather than individual identities.
- Multi-Factor Authentication (MFA): Require additional verification steps for sensitive actions.
- Service Accounts: Use dedicated identities for applications to avoid sharing human credentials.
Financial Governance
Cloud costs can spiral without visibility. Financial governance involves tracking spend against budgets and optimizing resource usage.
- Budget Alerts: Set thresholds that trigger notifications when spending approaches limits.
- Resource Scheduling: Automate the shutdown of development environments during non-working hours.
- Reserved Capacity: Purchase committed usage plans for predictable workloads to reduce rates.
Security and Compliance Integration 🔒
Security in the cloud differs from traditional data centers. Responsibility is shared between the provider and the consumer. The architecture must clearly delineate where these responsibilities begin and end.
Data Protection Strategies
Data is the most valuable asset. Protection strategies must cover the entire lifecycle, from creation to deletion.
- Encryption Standards: Use industry-standard algorithms for data at rest and in transit.
- Key Management: Centralize the management of encryption keys, allowing for rotation and revocation.
- Data Classification: Label data based on sensitivity to apply appropriate protection levels.
Threat Detection and Response
Defending against threats requires continuous visibility. Security operations centers (SOCs) must integrate with cloud logs to detect anomalies.
- Log Aggregation: Collect logs from all services into a central, immutable store.
- Anomaly Detection: Use machine learning to identify unusual patterns in traffic or access.
- Incident Response Playbooks: Prepare automated scripts to isolate compromised resources immediately.
Compliance Mapping
Regulatory requirements such as GDPR, HIPAA, or SOC2 dictate specific controls. The architecture must support these requirements out of the box.
- Region Selection: Host data in specific geographic locations to meet residency laws.
- Audit Trails: Maintain immutable logs of all administrative actions.
- Third-Party Validation: Engage auditors to verify compliance controls annually.
Cost Management and Optimization 💰
Cloud economics differ significantly from capital expenditure (CapEx) models. Operational expenditure (OpEx) models require continuous attention to ensure value.
The FinOps Approach
Financial Operations (FinOps) brings financial accountability to the variable spending model of the cloud. It requires collaboration between finance, engineering, and business teams.
- Cultural Shift: Empower engineers to understand the cost of the resources they provision.
- Real-Time Visibility: Provide dashboards that show cost by project, team, or application.
- Accountability: Assign cost ownership to specific teams rather than a central IT budget.
Optimization Techniques
Optimization is an ongoing process, not a one-time event.
- Right-Sizing: Adjust instance sizes to match actual workload requirements.
- Storage Tiering: Move infrequently accessed data to cheaper storage classes.
- Auto-Scaling: Ensure capacity matches demand dynamically to avoid over-provisioning.
Organizational Readiness and Culture 🤝
Technology alone does not guarantee success. The organization must be prepared to operate in a cloud-native way. This involves changing workflows, tools, and mindsets.
DevOps and Agile Practices
Cloud architectures enable faster delivery cycles. Teams should adopt DevOps practices to automate the software delivery pipeline.
- Continuous Integration/Continuous Deployment (CI/CD): Automate testing and deployment to reduce friction.
- Infrastructure as Code (IaC): Manage infrastructure using version-controlled code to ensure consistency.
- Collaboration: Break down silos between development and operations teams.
Skill Development
Legacy skills are insufficient for cloud environments. Training programs must be established to upskill the workforce.
- Cloud Certifications: Encourage staff to obtain relevant technical certifications.
- Internal Workshops: Share knowledge through internal tech talks and brown bags.
- External Partnerships: Leverage consultants or managed service providers for specialized expertise.
Measuring Success and KPIs 📈
To ensure the strategy is delivering value, key performance indicators (KPIs) must be defined and tracked. These metrics should reflect business outcomes, not just technical status.
Operational Metrics
- Availability: Percentage of time services are operational (e.g., 99.99%).
- Recovery Time Objective (RTO): Target time to restore services after a failure.
- Change Failure Rate: Percentage of deployments that cause service degradation.
Business Metrics
- Time to Market: Speed at which new features reach customers.
- Cost per Transaction: Efficiency of infrastructure relative to business volume.
- User Satisfaction: Feedback scores related to application performance.
Risk Mitigation Table
| Risk Area | Mitigation Strategy | Control Mechanism |
|---|---|---|
| Vendor Lock-in | Use open standards and abstraction layers | Portability Tests |
| Cost Overruns | Implement budget alerts and tagging policies | Automated Shutdown Scripts |
| Security Breach | Zero Trust Architecture and Encryption | Continuous Compliance Scanning |
| Service Outage | Multiregion deployment and backups | Disaster Recovery Drills |
Conclusion and Next Steps 🚀
Building a cloud-first enterprise architecture is a journey that requires patience, discipline, and continuous improvement. It involves aligning technology with business strategy, enforcing governance through automation, and fostering a culture of innovation.
Organizations that succeed in this space do not just move to the cloud; they transform how they create value. By focusing on flexibility, control, and operational excellence, businesses can build systems that are resilient to change and capable of supporting future growth.
Start by assessing your current state, define clear principles, and invest in the people who will build and maintain your future infrastructure. The path forward is clear, but it requires commitment at every level of the organization.
